Open source CMS (content management systems) are widely used because they are free, flexible and powerful, such as WordPressDrupal, Joomla etc. However, as the number of users grows, they also become the target of hackers. So, is open source CMS actually safe? And how to prevent being invaded?
![Image [1]-Open source CMS security analysis and protection guide: to avoid website intrusion](https://www.361sale.com/wp-content/uploads/2025/10/20251010110731534-image.png)
One,Open Source CMSsafety of
Open source does not mean insecure. Because the source code is public, security experts and community developers can quickly find and fix vulnerabilities. The real risks often come from the users themselves, for example:
- Not updating the system for a long time;
- Installation of plug-ins from unknown sources;
- Use a weak password or the default backend address.
Therefore, security depends more on the level of management of the site maintainer than on the system itself.
II. Common security risks
- weak password login: Simple passwords are highly vulnerable to brute force.
- plug-in vulnerability: Third-party plug-ins that are not maintained may be utilized by hackers.
- SQL Injection and File Upload Vulnerability: Unfiltered inputs or insecure upload mechanisms can lead to database breaches.
- Cross-site scripting attacks (XSS): Attackers insert malicious code into comments or forms to steal user information.
III. Effective methods of protection
1. Keep systems and plug-ins up to date
Most attacks originate from older version vulnerabilities. Core programs and plug-ins should be updated regularly, and automatic updates should be enabled to reduce delays in manual maintenance.
2. Use of strong passwords and double authentication
The administrator password should contain upper and lower case letters, numbers and special symbols, and be no less than 12 digits long. Double authentication (2FA) is also enabled so that it is difficult to be logged in illegally even if the password is leaked.
3. Installation of security plug-ins
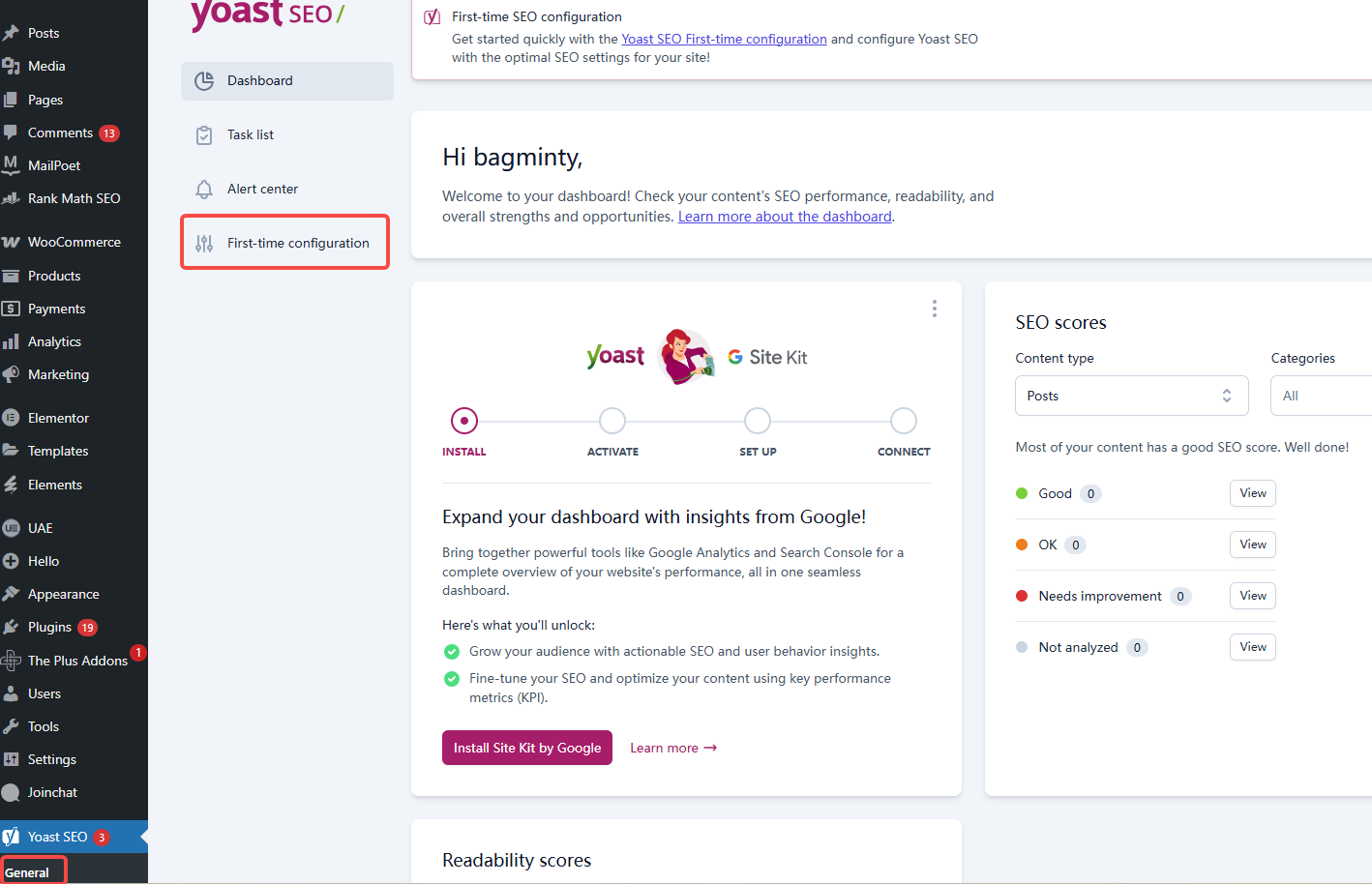
Open source CMSs usually support security plugins, for example:
- Wordfence Security: Monitor malicious logins and block suspicious IPs.
![Image [2]-Open source CMS security analysis and protection guide: to avoid website intrusion](https://www.361sale.com/wp-content/uploads/2025/10/20251010110801452-image.png)
- iThemes Security: Limit the number of logins, hide background paths.
![Image [3]-Open source CMS security analysis and protection guide: to avoid website intrusion](https://www.361sale.com/wp-content/uploads/2025/10/20251010110924708-image.png)
- Sucuri Security: Provides a firewall with real-time security scanning.
![Image [4]-Open source CMS security analysis and protection guide: to avoid website intrusion](https://www.361sale.com/wp-content/uploads/2025/10/20251010111026960-image.png)
These tools can automatically detect potential threats and issue alerts.
4. Regular backup of the website
No security measure is 100% reliable. It is recommended to automatically back up your database and website files on a daily basis and store the backups on a separate server or in the cloud. In case the website is hacked, it can be recovered quickly.
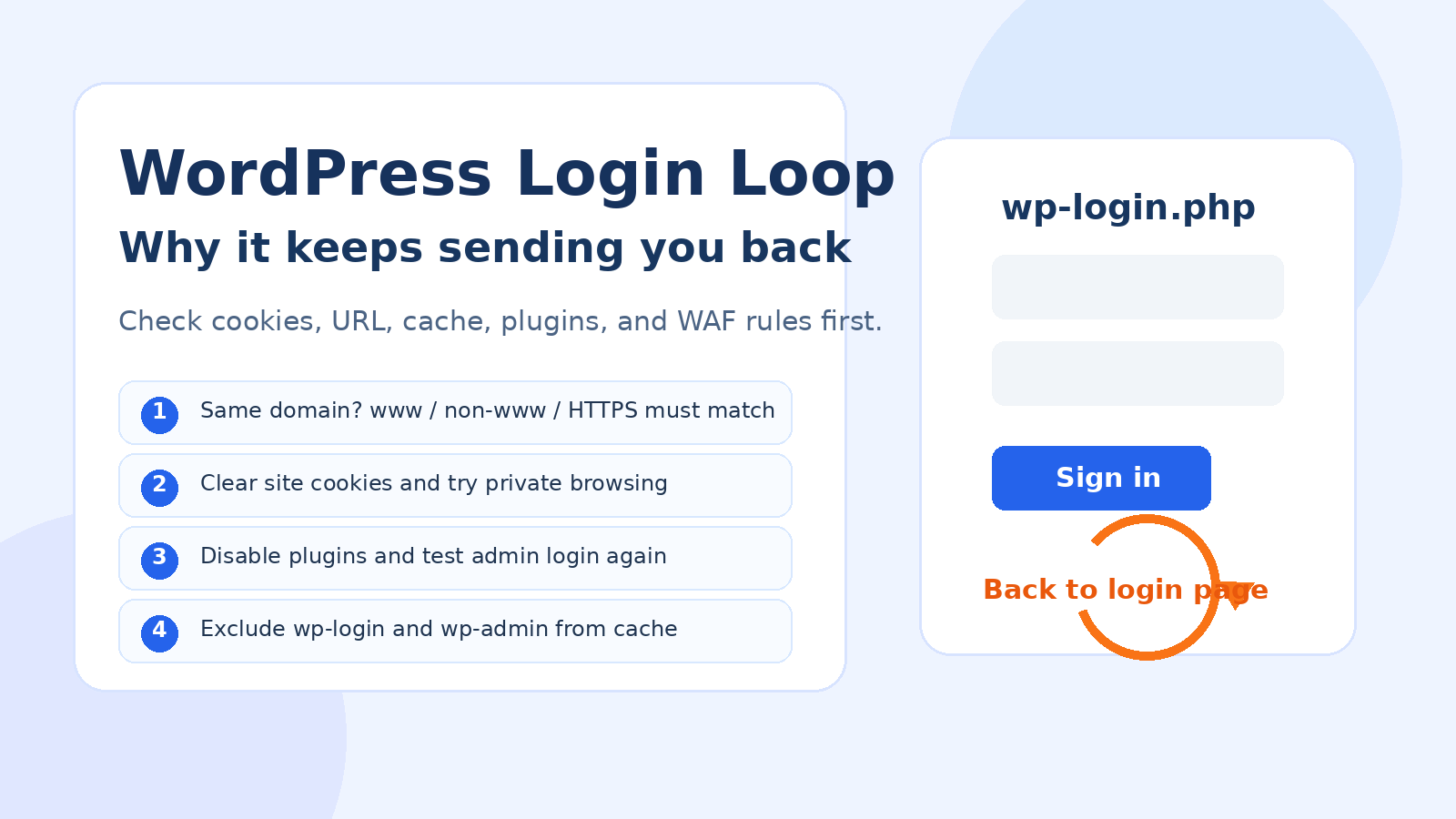
5. Restriction of back-office access
Modify the default backend path (e.g. WordPress (used form a nominal expression) /wp-admin) and set IP access restrictions. If possible, add a CAPTCHA or login protection plug-in.
6. Disabling unnecessary functions
If there is no need for open registration, file uploads or XML-RPC functionality, it's best to turn it off in the background. By reducing the number of entrances, you reduce the risk.
7. Use of HTTPS encryption
mountingSSLWith a certificate, website data is encrypted in transit, preventing hackers from intercepting or tampering with the information. Most hosts now offer free certificates, which are very simple to enable.
![Image [5]-Open source CMS security analysis and protection guide: to avoid website intrusion](https://www.361sale.com/wp-content/uploads/2025/10/20251010111110502-image.png)
8. Control of document permissions
Permissions on server files should be as strict as possible. For example, configuration files are read-only and upload directories are not executable. Excessive permissions can be exploited to execute malicious commands.
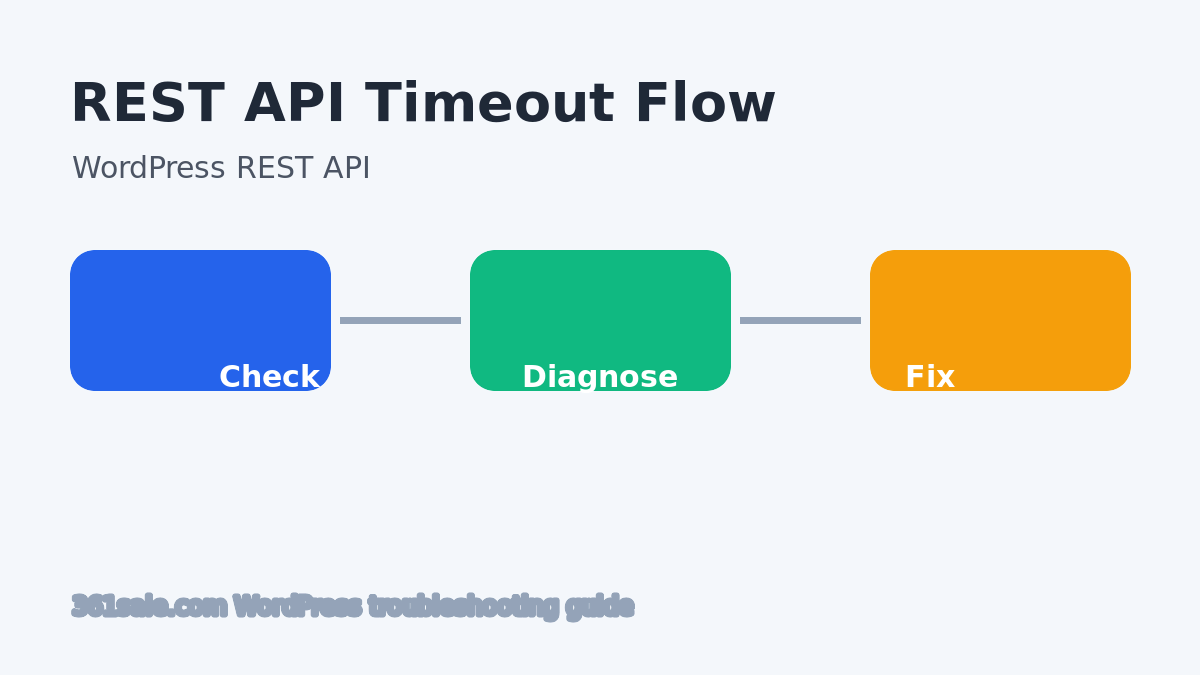
9. Regular security scans
Online tools such as SiteLock, Quttera or plug-ins with built-in scanning can be used to detect the presence of malicious code or tampered files on a weekly basis.
IV. Summary
Open Source CMSIt's not inherently vulnerable; the key is maintenance. By keeping it up to date, using secure plug-ins, reinforcing passwords, and making good backups, you can greatly reduce the risk of being compromised.
Security management is not a one-time task, but an ongoing process. For every website, prevention is far more important than fixing things after the fact.
Link to this article:https://www.361sale.com/en/78281/The article is copyrighted and must be reproduced with attribution.


















![Emoji[wozuimei]-Photonflux.com | Professional WordPress repair service, worldwide, rapid response](https://www.361sale.com/wp-content/themes/zibll/img/smilies/wozuimei.gif)
![Emoticon[baoquan] - Photon Wave Network | Professional WordPress Repair Services, Worldwide Coverage, Rapid Response](https://www.361sale.com/wp-content/themes/zibll/img/smilies/baoquan.gif)







No comments