It is well known that CAPTCHA (CAPTCHA) is the first line of defense in guarding the security of your WordPress site and is designed to differentiate between human users and automated programs (bots). Is your CAPTCHA really secure? In this article, we'll take a closer look at the most common methods attackers use to "crack" or bypass WordPress CAPTCHA and reveal the deadly risks behind them, with the aim of helping you build a stronger security barrier from a defender's point of view.
![Image [1] - Don't let bots devour your website! CAPTCHA Bypass Techniques Revealed & Ultimate Protection Guide](https://www.361sale.com/wp-content/uploads/2025/10/20251021142420674-image.png)
I. How do attackers "crack"? The most common 5 bypass methods
So-called "cracking" is rarely about actually breaking the CAPTCHA algorithm, but more about exploiting systemic vulnerabilities and weaknesses to "bypass" it.
1.OCR technology recognition against AI
- principle::OCR(Optical Character Recognition) technology is the classic method for recognizing traditional image CAPTCHAs. Attackers use a script to automatically download the CAPTCHA image, then parse it through a sophisticated OCR library (such as Tesseract) or a more advanced AI image recognition model to convert the characters in the image to text, which is then automatically submitted.
- Applicable objects: Traditional image CAPTCHA with distorted, sticky characters.
- status quo: With AI, even CAPTCHAs with added distracting lines and background noise can be easily cracked by trained models. This is exactly why new types of CAPTCHAs like reCAPTCHA are on the rise.
![Image [2] - Don't let bots devour your website! CAPTCHA Bypass Techniques Revealed & Ultimate Protection Guide](https://www.361sale.com/wp-content/uploads/2025/10/20251021142601722-image.png)
2.Captcha API Economy and Manual Coding Platforms
- principleThis is by far the most common and "efficient" way of bypassing the CAPTCHA. When an attacker's script encounters a CAPTCHA, it submits its image or question to a specialized "coding platform". Behind these platforms are a large number of cheap human workers who manually recognize the CAPTCHA in a very short period of time (usually a few seconds) and return the result to the attacker script via an API. The whole process is highly automated and very low-cost.
- Applicable objects: Almost any type of CAPTCHA, including logic questions, click-to-match images, and more.
- risk level: extremely high. This approach transforms a technical problem into an economic problem that is almost insoluble if the cost is low enough.
![Image [3] - Don't let bots devour your website! CAPTCHA Bypass Techniques Revealed & Ultimate Protection Guide](https://www.361sale.com/wp-content/uploads/2025/10/20251021142929903-image.png)
3.Exploiting website logic vulnerabilities and code flaws
- principle: This approach completely ignores the complexity of the CAPTCHA itself and attacks the "workflow" of the CAPTCHA verification process. For example:
- Front-end validation: CAPTCHA is only validated on the browser side with JavaScript, and requests submitted to the server side may lack secondary validation.
- Session mishandling: A vulnerability in the binding of the CAPTCHA to the server-side Session allows the same CAPTCHA to be reused, or Session checks to be bypassed.
- parameter tampering: Analyzed by a packet grabber toolHTTPrequest, directly modifying or skipping the parameters for submitting the CAPTCHA.
- Applicable objects: Develop custom CAPTCHAs or plugins that are not rigorous and have logic holes.
![Image [4] - Don't let bots devour your website! CAPTCHA Bypass Techniques Revealed & Ultimate Protection Guide](https://www.361sale.com/wp-content/uploads/2025/10/20251021144045851-image.png)
4.Automation Script Abuse and Browser Automation Tools
- principle: Using advanced browser automation tools like Selenium, Puppeteer, etc., you can simulate the behavior of real users. They can wait for the CAPTCHA to load and try to complete the challenge with some simple image recognition or pre-built interaction logic. While the success rate is not high for complex CAPTCHAs, they are still effective for simple math problems, clicking on specific buttons, etc.
- Applicable objects: Custom CAPTCHAs with simple logic and pages that lack other secondary safeguards.
5.Traffic masquerading and IP address pool rotation
- principle: This is not a direct bypass of the CAPTCHA, but rather an attempt to circumvent the limitations on how often the CAPTCHA can be triggered. The attacker uses a large pool of proxy IP addresses, rotating a different IP for each request, making it impossible for the site's security system to recognize that a particular IP has initiated a large number of requests in a short period of time, thus avoiding being forced to enter a CAPTCHA or being blocked outright.
- Applicable objects: All CAPTCHA systems with frequency limits.
II. The deadly risk behind "crack": much more than spam comments
![Image [5] - Don't let bots devour your website! CAPTCHA Bypass Techniques Revealed & Ultimate Protection Guide](https://www.361sale.com/wp-content/uploads/2025/10/20251021145326649-image.png)
When an attacker succeeds in bypassing CAPTCHA, your website is wide open to a host of serious security threats.
1.brute force attack (Brute Force)
CAPTCHA is the key to preventing brute force decryption of login pages and password reset pages. Once bypassed, an attacker can try thousands of username and password combinations indefinitely until the administrator's account is breached, resulting in a complete takeover of your site.
2.Spam comments and malicious registrations proliferate
This is the most intuitive consequence. Bots can post comments with spammy links in bulk or create tons of spammy user accounts on a site, which not only affects the quality of the site's content, but also damages the site's credibility with search engines.
3.Form content submission abuse
Attackers can automate the submission of contact forms, inquiry forms, and even utilize theWooCommerceThe website's coupon application function for woolgathering. This is not only a waste of server resources, but may also result in genuine user feedback being drowned out.
4.Resource exhaustion and DDoS attacks
A large number of automated requests can drastically consume the server's CPU and bandwidth resources, which may result in slower website response or even outright downtime, closing the door to normal users.
5.Data Scraping and Content Plagiarism
After bypassing the CAPTCHA, attackers can unscrupulously grab original content, product information, pricing data, etc. of a website and use it for unfair competition or to set up a mirror website.
Third, the way of defense: from "relying on CAPTCHA" to "defense in depth".
Understanding the means and risks of attacks, smart webmasters should build a multi-layered security system.
1.Ditch the old CAPTCHA and embrace smart, senseless authentication
Stop using simple image captchas immediately. Turn toGoogle reCAPTCHA v3 maybe Cloudflare Turnstile. They analyze a user's interaction with a website (e.g., mouse movements, clicking patterns) to give a risk score that is completely insensitive to the vast majority of normal users, yet accurately identifies bots.
![Image [6] - Don't let bots devour your website! CAPTCHA Bypass Techniques Revealed & Ultimate Protection Guide](https://www.361sale.com/wp-content/uploads/2025/10/20251021145102325-image.png)
2.Enforcement of strict frequency limits on visits
At the server level (e.g. Nginx) or through security plugins, there are strict limits on login attempts, form submissions, and other sensitive operations per IP address per unit of time. This is the cornerstone of defense against brute-force cracking and script abuse.
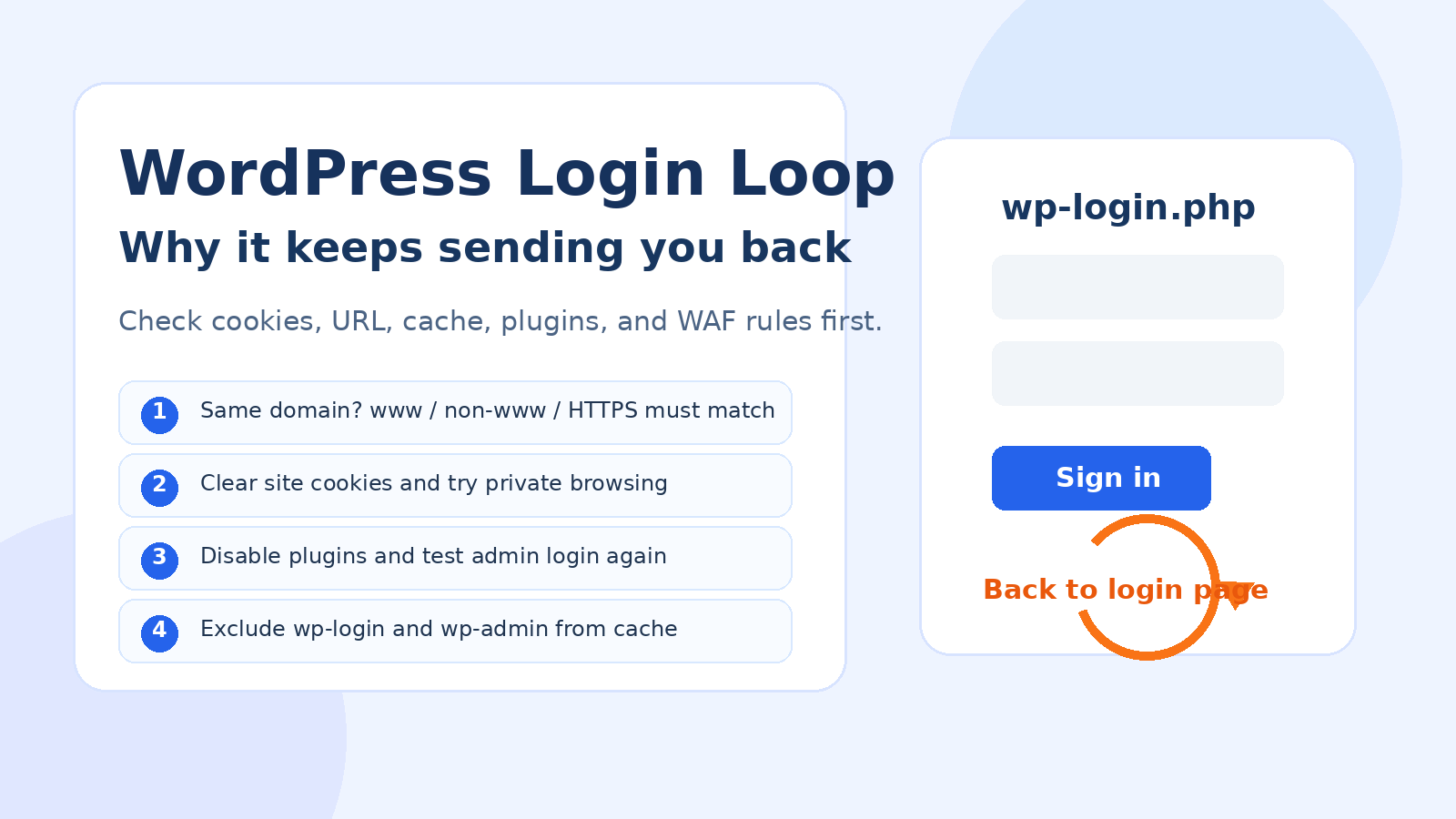
3.Deploying a Professional WordPress Security Plugin
e.g. using Wordfence Security maybe All In One Security (AIOS) and other plug-ins. They offer Web Application Firewall (WAF) functionality to identify and block malicious traffic, as well as advanced features such as login attempt limitations, hidden login address (wp-admin), and more.
![Image [7] - Don't let bots devour your website! CAPTCHA Bypass Techniques Revealed & Ultimate Protection Guide](https://www.361sale.com/wp-content/uploads/2025/10/20251021145934626-image.png)
4.Regular audits and updates
Regularly checked and updatedWordPresscore, themes and plugins to ensure that no known vulnerabilities are being exploited. Also, review website logs for unusual access patterns.
5.Enhanced server-level configuration
For websites with high security requirements, consider configuring tools such as Fail2ban, which automatically analyzes logs and adds IP addresses with malicious behavior to the firewall blacklist.
reach a verdict
"Crack."WordPressThe technical barriers to CAPTCHA are constantly being lowered, which requires us to take an evolutionary view of website security. A single CAPTCHA has long been a panacea. True security lies in building aDefense in Depth (DID) system-- Combines multiple means of intelligent authentication, frequency restrictions, firewalls, regular maintenance, and strong password policies.
The only way to ensure that yourWordPressWebsites stand tall against the digital tides. Remember, security is not a feature, but an ongoing process.
Link to this article:https://www.361sale.com/en/78912/The article is copyrighted and must be reproduced with attribution.


















![Emoji[wozuimei]-Photonflux.com | Professional WordPress repair service, worldwide, rapid response](https://www.361sale.com/wp-content/themes/zibll/img/smilies/wozuimei.gif)
![Emoticon[baoquan] - Photon Wave Network | Professional WordPress Repair Services, Worldwide Coverage, Rapid Response](https://www.361sale.com/wp-content/themes/zibll/img/smilies/baoquan.gif)







No comments