existWordPressSpam protection is an important work for webmasters in website operation. The current mainstream anti-spam plug-ins have the problems of large resource consumption and lack of compatibility, and some plug-ins may also bring security risks. This article provides five pure-code solutions, which are directly integrated into the website system and can effectively improve the protection ability and realize more secure and efficient anti-spam management.

I. The honeypot technique: the art of the invisible trap
honeypot technologyIt is an efficient and user-insensitive anti-spam tool. It works by setting a trap field that is invisible to human users but visible to spam bots, and when the field is filled in it is determined to be spam.
1.1 Comment form honeypot implementation
Add the following code to the theme's functions.php file:
function add_honeypot_field($fields) {
$fields['honeypot'] = '<p class="hp-wrap" style="display: none;"><label>Please do not fill in this field</label><input type="text" name="honeypot" value="" /></p>';
return $fields.
}
add_filter('comment_form_default_fields', 'add_honeypot_field');
function check_honeypot() {
if(!empty($_POST['honeypot'])) {
wp_die('Spam submission detected');
}
}
add_action('pre_comment_on_post', 'check_honeypot');1.2 Analysis of technical principles
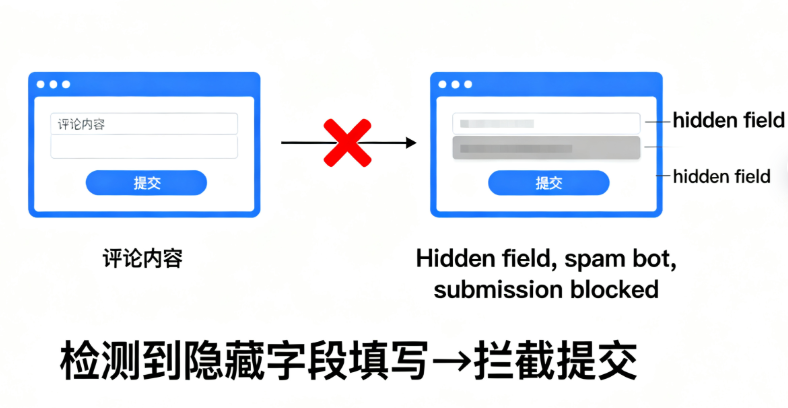
This code creates a file in the comment form that is passed through theCSSHidden input fields that normal users cannot see and will not fill out. Automated spambots typically fill in all form fields found, including this hidden field. When the system detects that this hidden field is being filled in, it automatically blocks the submission.
II. Timestamp verification: a time-based protection strategy
Capitalizing on the significant difference in form-filling speed between human users and bots, timestamp validation can effectively identify and block automated submissions.
2.1 Implementation of time-based validation mechanisms
existfunctions.phpAdd time validation logic to the
function add_timestamp_field() {
echo '';
}
add_action('comment_form', 'add_timestamp_field');
function verify_timestamp() {
if(isset($_POST['timestamp'])) {
$submission_time = time() - intval($_POST['timestamp']);
if($submission_time < 5) {
wp_die('Submission was too fast, please try again later');
}
}
}
add_action('pre_comment_on_post', 'verify_timestamp');2.2 Parameter tuning and optimization

The key to this scheme is the setting of the time threshold. Usually 5-10 seconds is a reasonable range to block bots without affecting normal comments from real users. For different types of websites, this threshold can be adjusted according to actual needs.
III. Mathematical problem validation: simple and effective interactive validation
Adding simple math calculation problems to a form can effectively differentiate between a human user and an automated program.
3.1 Mathematical verification function implementation
function add_math_question() {
$num1 = rand(1, 10);
$num2 = rand(1, 10);
echo '<p>Please answer: '.$num1.' + '.$num2.' = ?<br /><input type="text" name="math_answer" />'; echo '
echo '<input type="hidden" name="math_problem" value="'.($num1 + $num2).'" /></p>';
}
add_action('comment_form', 'add_math_question');
function verify_math_answer() {
if(isset($_POST['math_answer']) && isset($_POST['math_problem'])) {
if(intval($_POST['math_answer']) ! == intval($_POST['math_problem'])) {
wp_die('Wrong answer, please return for recalculation');
}
}
}
add_action('pre_comment_on_post', 'verify_math_answer'); }3.2 User experience considerations

While mathematical validation adds steps for the user, extremely simple arithmetic problems do not significantly impact the user experience. This solution is particularly suitable for personal blogs or business websites with a small number of comments.
IV. Keyword filtering system: precision strikes at the content level
Create a custom keyword blacklist to scan and filter comment content in real time.
4.1 Blacklist Filtering Mechanisms
function custom_keyword_filter($commentdata) {
$blacklist = array('赌博', '彩票', '色情', '违禁品');
$content = $commentdata['comment_content'];
foreach($blacklist as $keyword) {
if(strpos($content, $keyword) !== false) {
wp_die('评论包含禁止内容:'.$keyword);
}
}
return $commentdata;
}
add_filter('preprocess_comment', 'custom_keyword_filter');4.2 Dynamic blacklist management

To increase flexibility, the blacklist can be stored in a database or configuration file for easy updating at any time. For high-traffic websites, it is recommended to incorporate a caching mechanism to optimize performance.
V. User behavior analysis: intelligent protection based on pattern recognition
Identify and block suspicious spam submission patterns by analyzing user submission behavior characteristics.
5.1 Multi-dimensional Behavior Detection
function advanced_spam_detection($commentdata) {
// Detection of link count
$link_count = preg_match_all('/https?:\/\/[^\s]+/', $commentdata['comment_content']);
if($link_count > 2) {
wp_die('comment contains too many links');
}
// Detect duplicate content
$content_hash = md5($commentdata['comment_content']);
if(get_transient('comment_hash_'.$content_hash)) {
wp_die('Duplicate comment detected');
}
set_transient('comment_hash_'.$content_hash, true, 3600);
return $commentdata;
}
add_filter('preprocess_comment', 'advanced_spam_detection');5.2 Pattern Recognition Optimization
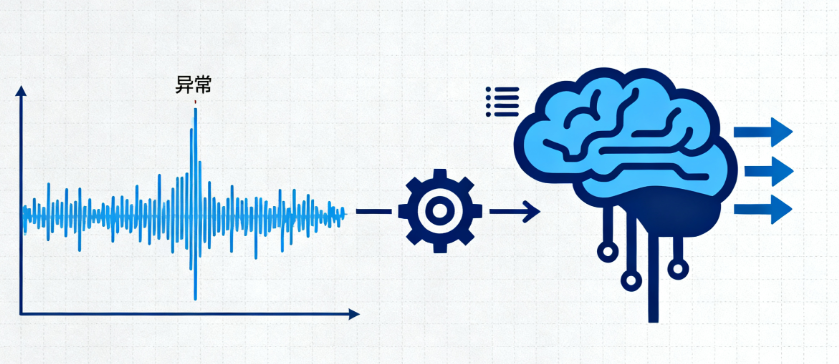
This solution can be further extended to include detecting comment frequency, analyzing content features, and more. The detection accuracy can be continuously optimized through machine learning algorithms.
VI. Comprehensive implementation program and best practices
Using any one program alone has its limitations, and combining multiple approaches is the best way to achieve optimal results.
6.1 Recommendations for program mix
It is recommended to use at least both honeypot techniques and timestamp verification, both of which are completely transparent to users and highly effective. For sites that are particularly spammy, additional verification with math problems can be added.
6.2 Performance Monitoring and Tuning
After implementing these programs, the site's comments need to be closely monitored. Regularly check the error logs to see if any false intercepts are occurring and adjust the relevant parameters accordingly.
6.3 Continuous Improvement Strategy
Spamming techniques are also evolving and require regular updates to protection strategies. Keep an eye on the latest spam features and adjust keyword lists and detection algorithms in a timely manner.
By implementing these code-only solutions, you can not only effectively reduce the nuisance of spam, but also improve the performance of your website and avoid various potential problems caused by plug-ins. These solutions can be flexibly combined according to the specific needs of the website to build a solid anti-spam protection system.
Link to this article:https://www.361sale.com/en/79741/The article is copyrighted and must be reproduced with attribution.





















![Emoji[wozuimei]-Photonflux.com | Professional WordPress repair service, worldwide, rapid response](https://www.361sale.com/wp-content/themes/zibll/img/smilies/wozuimei.gif)
![Emoticon[baoquan] - Photon Wave Network | Professional WordPress Repair Services, Worldwide Coverage, Rapid Response](https://www.361sale.com/wp-content/themes/zibll/img/smilies/baoquan.gif)







No comments