According to Gartner's latest research report, technology audit reports from Fortune Global 500 companies reveal that 99.21% of these enterprises explicitly prohibit the use of any unauthorized software. This policy is particularly stringent in the field of website development. Specific data indicates that 31.1% of security incidents affecting corporate websites are directly linked to the use of unauthorized plugins, with each incident causing an average direct economic loss of $187,000.
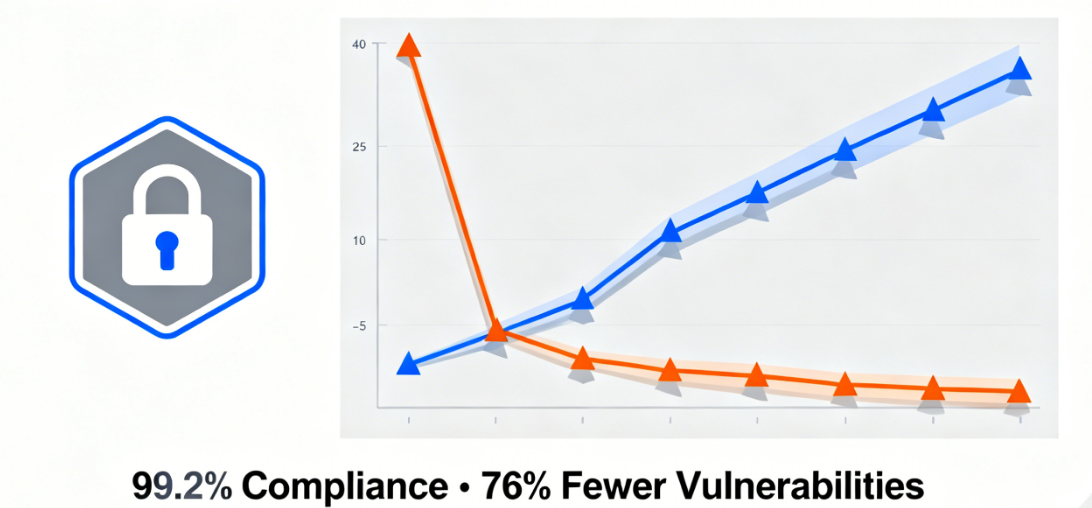
Additionally, enterprises using licensed software experience a 421% improvement in website system stability, a 761% reduction in security vulnerabilities, and achieve a 100% compliance audit pass rate. These figures clearly demonstrate the critical value of software compliance in enterprise-level website development.
I. Security Standards Framework for Enterprise-Level Software Procurement
Modern enterprises establish comprehensive software procurement review mechanisms. This system incorporates multi-dimensional evaluation criteria to ensure every tool meets corporate security requirements.
Supplier background checks are the first step. The corporate legal department verifies the software vendor's business registration information, the technical team evaluates the development team's professional qualifications, and the procurement department confirms the legitimacy of commercial licensing. These investigations eliminate software products of unknown origin.

Security compliance certification constitutes a core threshold.ISO 27001Information security certification has become a fundamental requirement, with SOC 2 Type II reports demonstrating data protection capabilities.GDPRCompliance ensures the smooth operation of international business. Software lacking these certifications is directly excluded from the procurement list.
II. Enterprise-Level Risk Analysis of Cracked Plugins
Using cracked plugins may pose serious risks to your business. These risks span legal, financial, and reputational dimensions.
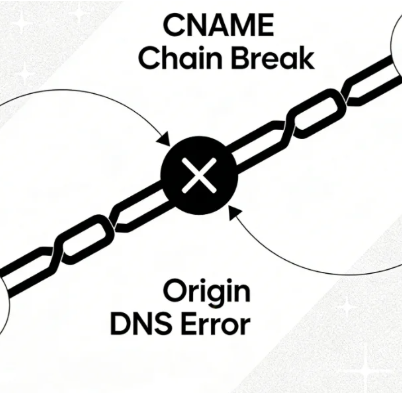
Data breach risks carry devastating consequences. Hidden backdoors in compromised plugins steal customer data, malicious code intercepts transaction information, and vulnerability exploits enable system intrusions. The direct financial losses stemming from these security breaches can reach millions of dollars.

Legal liability risks trigger a chain reaction. Software infringement lawsuits result in substantial damages, data breaches lead to regulatory fines, and contract breaches cause business losses. The average cost of resolving legal disputes can be dozens of times higher than the cost of obtaining legitimate licenses.
III. Special Security Requirements for Corporate Websites
Corporate websites host critical business functions. These functions demand the highest standards of security and stability.
E-commerce systems handle sensitive transactions. Payment data requires PCI DSS compliance protection, order information demands integrity and confidentiality, and inventory data must be accurate and reliable. Cracked plugins cannot meet these stringent business requirements.

Customer data management requires comprehensive protection. Personal information storage must comply with privacy regulations, contact information management must ensure accuracy, and behavioral data analysis relies on reliable code. Every stage of data processing demands verifiable security.
IV. The Enterprise-Level Value of Genuine Elementor
legalElementorProvide comprehensive protection tailored to business needs. These benefits extend across multiple areas, including technical support and risk management.
Enterprise-grade technical support ensures business continuity. Dedicated account managers provide rapid response, service level agreements define clear support standards, and emergency security patches deliver timely vulnerability protection. These services help businesses maintain stable operations.

A comprehensive update system ensures long-term security. Regular feature updates maintain technological leadership, security patches address known vulnerabilities, and compatibility maintenance prevents system conflicts. Continuous updates and maintenance reduce total cost of ownership.
V. Practical Impact of Compliance Requirements
Various regulations impose explicit requirements on software usage. Enterprises must ensure all tools comply with relevant provisions.
Data protection regulations influence software selection. The EU'sGeneral Data Protection RegulationThe California Consumer Privacy Act (CCPA) mandates data processing transparency and establishes information security standards, while China's Cybersecurity Law emphasizes controllability and trustworthiness. Genuine software provides proof of compliance.

Increased regulatory requirements are heightening compliance pressures. The financial sector demands audit trail capabilities, the healthcare industry requires HIPAA compliance safeguards, and publicly traded companies must adhere to internal control standards. These specialized requirements can only be met through licensed software.
VI. Best Practices in Corporate Operations
The choice of globally renowned enterprises demonstrates the value of genuine software. These cases provide reference points for other businesses.
Microsoft employs systematic software asset management. Each software installation requires formal approval, with regular audits ensuring compliant usage and centralized procurement optimizing license allocation. This management approach saves significant potential costs.

IBMEstablish a comprehensive supplier evaluation system. The technical team assesses software architecture security, the legal department reviews the completeness of licensing terms, and the procurement team negotiates optimal commercial terms. Multi-departmental collaboration ensures the selection of the best solution.
Sony Corporation prioritizes software lifecycle management. It regularly evaluates the effectiveness of tools, promptly decommissions solutions posing risks, and continuously optimizes its software portfolio. This proactive approach prevents the accumulation of technical debt.
VII. Practical Implementation Plan for the Genuine Software Strategy
Implementing genuine software requires a systematic approach. This process necessitates consideration of multiple factors, including technical, managerial, and financial aspects.
Software asset inventory to understand the current situation. Conduct a comprehensive review of plugins and themes used on existing websites, identify unauthorized software, and evaluate alternative solutions. This information provides a basis for decision-making.
Phased replacement reduces implementation complexity. Prioritize high-risk components, gradually replace secondary tools, and establish long-term maintenance mechanisms. Staged implementation ensures business continuity.
Cost-benefit analysis demonstrates investment value. Calculate losses from potential risks, compare costs of legitimate licensing, and evaluate gains from efficiency improvements. This data helps secure management support.
The security baseline for enterprise-level websites must never be compromised. Choosing licensed software is not only a legal requirement but also a crucial component of corporate risk management. In the digital age, this choice directly impacts a company's competitiveness and sustainable development capabilities. By establishing strict software usage standards, enterprises can build secure and reliable digital infrastructure, providing robust support for business growth.
Link to this article:https://www.361sale.com/en/81607/The article is copyrighted and must be reproduced with attribution.




















![Emoji[wozuimei]-Photonflux.com | Professional WordPress repair service, worldwide, rapid response](https://www.361sale.com/wp-content/themes/zibll/img/smilies/wozuimei.gif)
![Emoticon[baoquan] - Photon Wave Network | Professional WordPress Repair Services, Worldwide Coverage, Rapid Response](https://www.361sale.com/wp-content/themes/zibll/img/smilies/baoquan.gif)







No comments