2026 WooCommerce The store has evolved from being a mere tool for trading goods to continuously processing Order data, customer privacy and payment callbacks of core business systems.Any security incidentAll may directly affect customer trust, payment compliance and search engine performance. This article focuses on real risk scenarios, and systematically explains how to pass theThe right combination of security plug-ins with the right configurationIn addition, the Government of the Republic of Korea will effectively protect the rights and interests of the people of the Republic of Korea in the year 2026. WooCommerce Order and Customer Data SecurityThe
![Image [1] - Don't wait to be hacked to regret it: the complete WooCommerce order and customer data security solution for 2026](https://www.361sale.com/wp-content/uploads/2026/01/20260107094313442-image.png)
I. Why WooCommerce stores must focus on security in 2026
1.1 E-commerce attacks have become highly automated
in the wake ofautomationThe proliferation of chemical tools and scripts for WooCommerce The attacks no longer rely on manual operations, but are done through bulk scanning and automated exploitation of vulnerabilities.
The target of the attack usually focuses on the following areas:
- Backstage Login Portal
- Checkout and Payment Interface
- Customer account page
- Order and User Data Sheets
Once successfully compromised, attackers often do not immediately expose their behavior, but continue to steal data or wait for the right moment to conduct a secondary attack.
![Image [2] - Don't wait to be hacked to regret it: a complete solution for WooCommerce order and customer data security in 2026](https://www.361sale.com/wp-content/uploads/2026/01/20260107094541135-image.png)
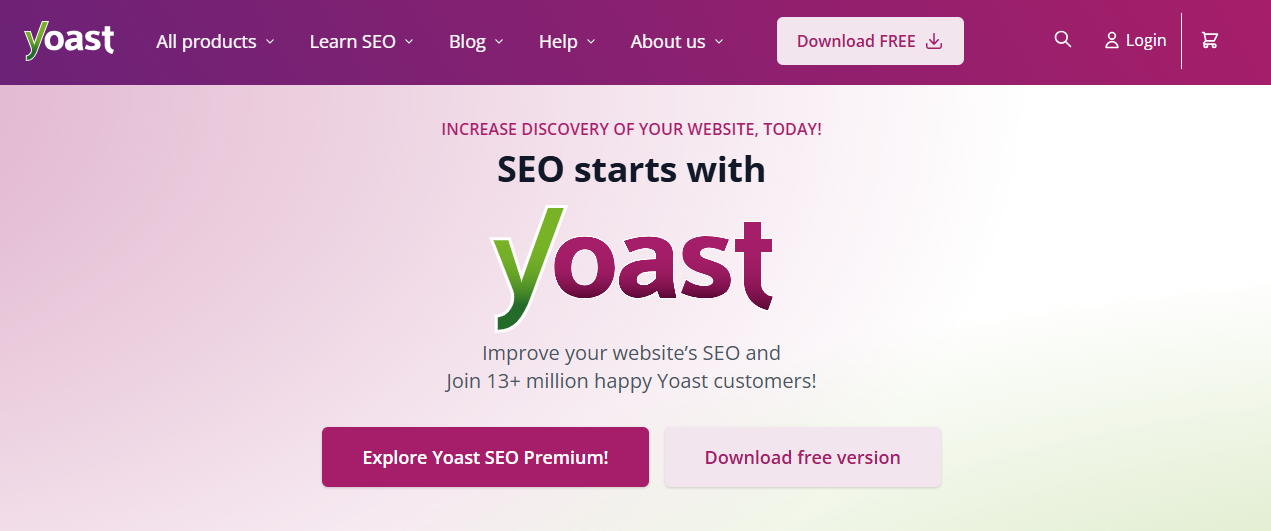
1.2 WooCommerce Common High-Risk Portals
In real-world operations, the following entry points are the most common points of attack in 2026:
| Entrance type | Risk description |
|---|---|
| Backend Login Page | Brute force cracking, voucher filling |
| Discontinued plug-ins | Published Vulnerabilities |
| XML-RPC interface | Remote Brute Force Request |
| REST API | The order interface has been abused |
| Improperly configured permissions | Internal misuse or overstepping of authority |
These risks are not theoretical issues, but rather a large number of real-life cases ofReasons for recurrenceThe
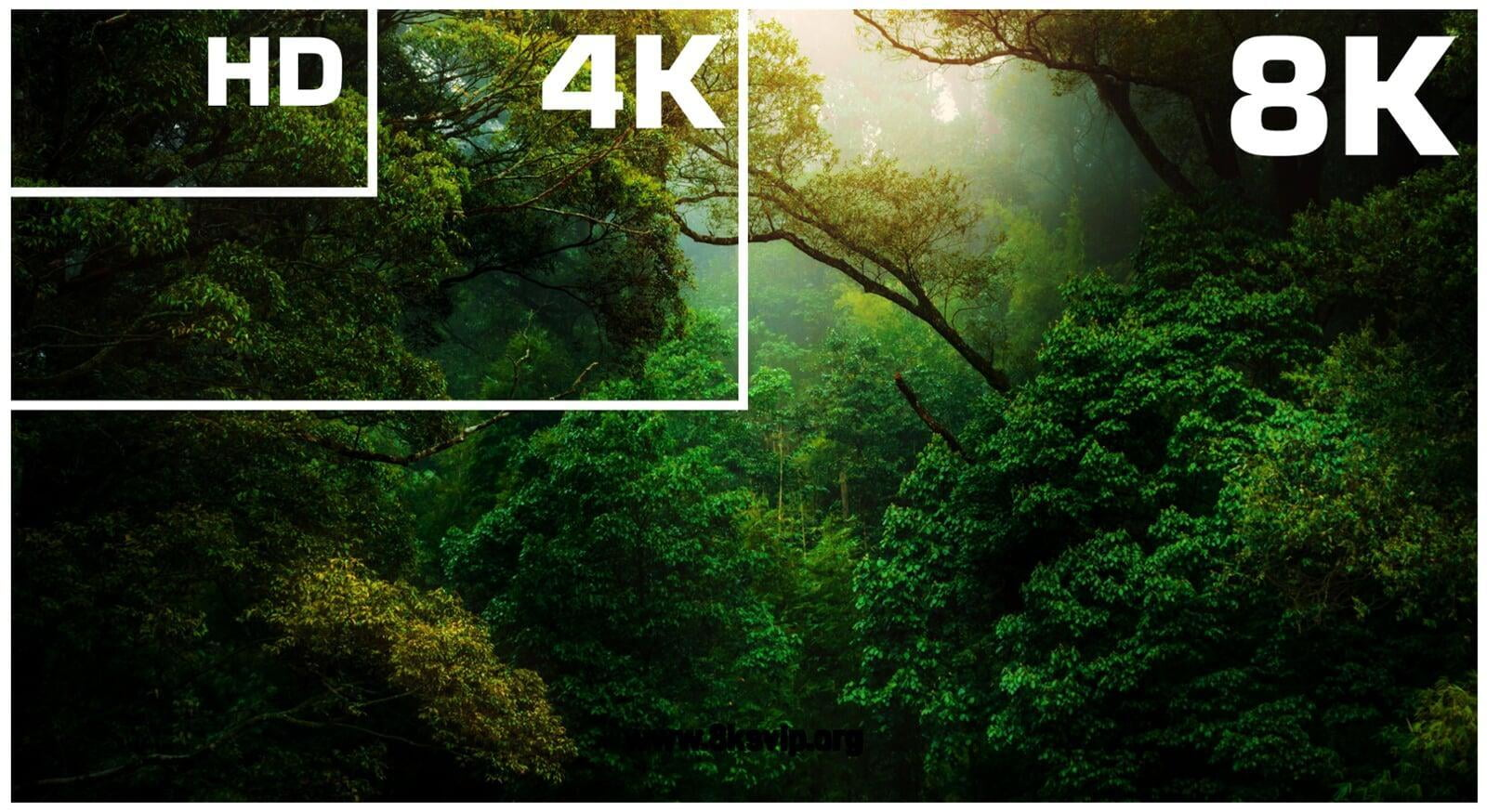
The Core Idea of WooCommerce Security: Layered Protection
In 2026, a single plug-in will no longer be able to cover all security needs.
WooCommerce suretyshould follow layered protection The basic idea is that each layer is responsible for a different type of risk.
2.1 Four critical layers of protection
| protection level | primary objective |
|---|---|
| firewall layer | Blocking malicious access and attack requests |
| scanning layer | Discovery of tampered files and malicious code |
| Login and Privilege Layer | Protecting back-end accounts and operating privileges |
| Data and Order Layer | Monitor and protect core business data |
It is around these four tiers that the subsequent recommended plugins are wisely combined.
III. Firewalls and intrusion prevention: the first line of security defense
3.1 Wordfence Security
Wordfence Security is currently one of the most mature security plugins in the WooCommerce ecosystem, primarily responsible for thefirewallswith real-time threat interception.
3.1.1 Core functions
- Web Application Firewall (WAF)
![Image [3] - Don't wait to be hacked to regret it: the complete WooCommerce order and customer data security solution for 2026](https://www.361sale.com/wp-content/uploads/2026/01/20260107095154957-image.png)
- Brute Force Protection
![Image [4] - Don't wait to be hacked to regret it: the complete WooCommerce order and customer data security solution for 2026](https://www.361sale.com/wp-content/uploads/2026/01/20260107095234682-image.png)
- SQL Injection and XSS Attack Blocking
- Real-time traffic and threat monitoring
![Image [5] - Don't wait to be hacked to regret it: the complete WooCommerce order and customer data security solution for 2026](https://www.361sale.com/wp-content/uploads/2026/01/20260107095335701-image.png)
3.1.2 Recommended configuration
Enable firewall mode
- In an Apache or LiteSpeed server environment, it is recommended that you enable the Extended Protection, for earlier request interception capabilities.
- In a Nginx environment, Wordfence operates as an application-layer firewall, and you need to ensure that its rules are in effect correctly and that it is used in conjunction with server or CDN protection.
Limit Login Attempts
- Set up automatic lockout for 3-5 failed login attempts
- Lockout time of not less than 4 hours
WooCommerce Interface Protection
- For actual use of the WooCommerce REST API (such as the
/wc/v3/,/wc/store/) Conducting Tests - Avoid mistakenly blocking payment callbacks and checkout requests
![Image [6] - Don't wait to be hacked to regret it: the complete WooCommerce order and customer data security solution for 2026](https://www.361sale.com/wp-content/uploads/2026/01/20260107094502643-image.png)
IV. Back-office structure and authority security
4.1 iThemes Security Pro
iThemes Security More focused on back-end structural security and privilege management, suitable for multi-person collaborative operations WooCommerce Store.
![Image [7] - Don't wait to get hacked to regret it: a complete WooCommerce order and customer data security solution for 2026](https://www.361sale.com/wp-content/uploads/2026/01/20260107100838296-image.png)
4.1.1 Main roles
- Hide default backend path
- Enforcing strong password policies
- Managing user rights and login behavior
4.1.2 Practical configuration recommendations
- Reduce the probability of being scanned by using a customized backend login address
- Enforce two-factor authentication (2FA) for the administrator role
- If you are not using remote publishing or management features, you can limit or disable XML-RPC; if you still need to use it, you should limit the frequency of requests through a firewall.
V. Order and customer data protection
5.1 Jetpack Security: Data Backup and Recovery
Jetpack The core value in the WooCommerce security system, theGuaranteed data recoverabilityThe
![Image [8] - Don't wait to be hacked to regret it: a complete WooCommerce order and customer data security solution for 2026](https://www.361sale.com/wp-content/uploads/2026/01/20260107100656844-image.png)
5.1.1 Why e-commerce must emphasize backups
Common risks include:
- Plugin update causes database exception
- server failure
- Need to roll back quickly after an intrusion
For e-commerce sites, theOnce order data is lost, it is almost impossible to regenerateThe
5.1.2 Recommended settings
- Enable WooCommerce Real-Time Order Backup
- Backup retention period of not less than 30 days
- Automatically create restore points before plugin updates or theme modifications
![Image [9] - Don't wait to get hacked to regret it: a complete WooCommerce order and customer data security solution for 2026](https://www.361sale.com/wp-content/uploads/2026/01/20260107100713851-image.png)
5.2 WP Activity Log: Operation and Order Audit
WP Activity Log It is an important tool used to record back-office behavior and order operations, and is gradually becoming a must-have plug-in in compliance and risk control scenarios.
![Image [10] - Don't wait to be hacked to regret it: the complete WooCommerce order and customer data security solution for 2026](https://www.361sale.com/wp-content/uploads/2026/01/20260107101020169-image.png)
5.2.1 Recordable content
- Order creation, modification and status change
- Adjustment of user rights
- Backend key operation log
![Image [11] - Don't wait to get hacked to regret it: a complete solution for WooCommerce order and customer data security in 2026](https://www.361sale.com/wp-content/uploads/2026/01/20260107100948666-image.png)
5.2.2 Configuration recommendations
- Enable WooCommerce-specific logging module
- Focus on monitoring administrators and advanced roles
- The recommended log retention time is not less than 90 days
VI. Security measures that must be synchronized outside the plug-in
6.1 Server and Network Layer
- Force HTTPS and use TLS 1.3
- Traffic filtering in conjunction with CDN services
- Setting Request Frequency Limits for the REST API
6.2 Plug-in management principles
- Regularly clean up plugins that are no longer maintained
- Control the number of plug-ins to avoid overlapping functionality
- No plug-ins from unknown sources or cracked versions
6.3 Principle of least privilege
- Administrator privileges are not granted to day-to-day operations staff
- Outsourced or temporary accounts set expiration times
- Separation of development and formal environment
![Image [12] - Don't wait to get hacked to regret it: the complete WooCommerce order and customer data security solution for 2026](https://www.361sale.com/wp-content/uploads/2026/01/20260107094349452-image.png)
Example of WooCommerce Security Plugin Portfolio
The following scenarios are reference combinations for common scenarios, and should be adjusted in conjunction with the server environment.
Standard e-commerce site
- Wordfence Security
- Jetpack Security
- WP Activity Log
Multi-collaboration or high order volume sites
- Wordfence Security
- iThemes Security Pro
- Jetpack Security
- WP Activity Log
Link to this article:https://www.361sale.com/en/85427The article is copyrighted and must be reproduced with attribution.














![Emoji[wozuimei]-Photonflux.com | Professional WordPress repair service, worldwide, rapid response](https://www.361sale.com/wp-content/themes/zibll/img/smilies/wozuimei.gif)
![Emoticon[baoquan] - Photon Wave Network | Professional WordPress Repair Services, Worldwide Coverage, Rapid Response](https://www.361sale.com/wp-content/themes/zibll/img/smilies/baoquan.gif)







No comments