LinktreeWith its efficient link management capabilities, it has become the tool of choice for many brands and creators to carry out their digital marketing strategies, and more than 50 million users around the world now rely on the platform for daily traffic distribution. However, while enjoying the convenience, about 79% users ignore the hidden privacy and security risks.
Industry reports show that third-party linking services have become a new risk point for data breaches, with resulting campaign disruptions growing by 42% last year.These risks can pose a serious threat to brand reputation and business continuity, with average losses of up to $15,000 per service disruption, according to statistics.
I. Clear boundaries of data ownership
When using third-party services, the definition of data ownership and access rights is a primary consideration.
1.1 Analysis of access to platform data
Linktree's terms and conditions as a service platform specify the processing rights for the collected data. This includes sensitive data such as visitors' click behavior, geolocation information, device type, and more. Brands need to carefully review the service agreement to understand whether the platform has the right to use aggregated data for business analytics or whether anonymized data may be shared with third parties.

1.2 Compliance Requirements for User Privacy Protection
Data protection regulations in different regions impose strict requirements for the collection of user information. The EU'sGeneral Data Protection Regulation(GDPR) and California'sConsumer Privacy ActThe CCPA sets clear standards for the collection, storage and processing of user data. When using services such as Linktree, it is important to ensure that they are operated in accordance with applicable privacy legislation or you may be exposed to legal risks.

II. Technical safeguards for link security
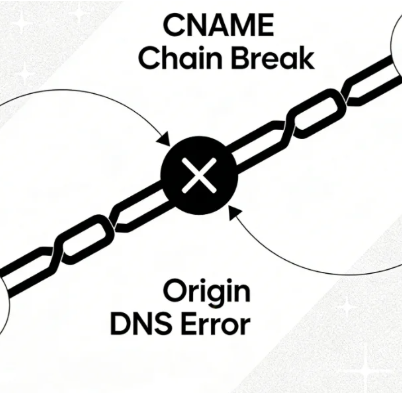
Security breaches in the link-hopping process can cause irreparable damage.
2.1 Prevention of Man-in-the-Middle Attacks
There is a risk of malicious interception during link hopping. Attackers may take advantage of insecure network environments to steal user information or plant malicious code during the hopping process. Adoption ofHTTPS encryptionThe protocol effectively prevents eavesdropping and tampering during data transmission and ensures the user's security from start to finish.

2.2 Security Value of Customized Domain Names
Binding a customized domain name is not only a reflection of brand professionalism, but also an important part of security. Use the official defaultlinktr.eeSubdomains are at risk of domain name spoofing and phishing. Own domain name cooperationSSL certificateThe implementation can establish a complete chain of trust and prevent users from being directed to malicious websites.
III. Risk management of service dependency
Over-reliance on a single service provider can present business continuity pitfalls.
3.1 Emergency preparedness for service disruptions
Third-party service platforms inevitably experience technical glitches or server downtime.2022 Linktree had a brief service outage that prevented a large number of users from properly accessing its linked pages. Such contingencies can bring ongoing marketing campaigns to a standstill, missing out on valuable conversion opportunities.
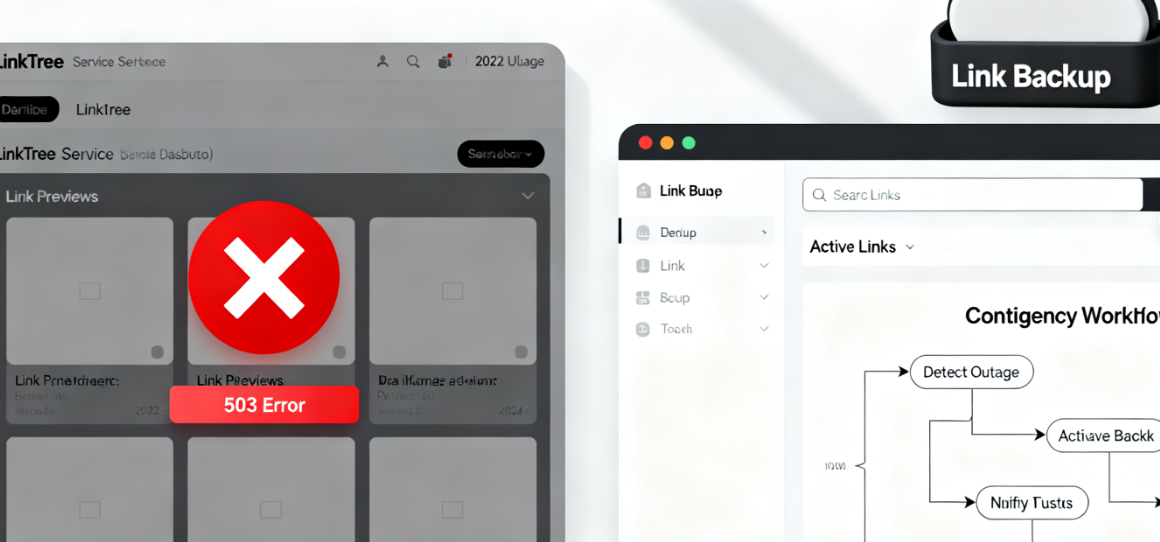
3.2 Principles for the establishment of options
Wise marketers should prepare contingency plans. This includes regularly backing up Linktree page settings, preparing alternative link management tools, and retaining direct access to core links in key promotional channels. In the event that the primary service fails, it can be quickly switched over to the backup solution to ensure business is up and running.
IV. Integrated risk management framework
Establishing a systematic risk management system is the only way to maximize the value of the tool while controlling potential threats.
4.1 Regular security audit mechanism
Quarterly security checks of Linktree accounts are recommended. Review access settings to ensure that former employees cannot continue to access the account. Check the security of all jump links to avoid pointing to pages that have been hacked. Review privacy policy changes and adjust data collection strategies in a timely manner.
4.2 Data Backup and Migration Strategy
Maintaining data independence and portability is critical. Regularly export Linktree's analytics data to prevent loss of historical data due to account anomalies or service changes. Also understand the specifics of the data migration process to ensure a smooth transition to other platforms when needed.
4.3 Team operation specification development
For the Linktree account used by the team, a clear operation specification needs to be established. Provide for the review process of adding links to avoid malicious links being added at will. Set up a hierarchical management system for different roles to enjoy different operating privileges. Establish an emergency response process to ensure that problems can be quickly and effectively responded to.
In the era of digital marketing, the choice of tools is not only about efficiency, but also directly affects the safety bottom line of the brand. By establishing a perfect risk management mechanism, we can enjoy the convenience of technology while guarding the rights and interests of brands and users.
Link to this article:https://www.361sale.com/en/80560The article is copyrighted and must be reproduced with attribution.
















![Emoji[wozuimei]-Photonflux.com | Professional WordPress repair service, worldwide, rapid response](https://www.361sale.com/wp-content/themes/zibll/img/smilies/wozuimei.gif)
![Emoticon[baoquan] - Photon Wave Network | Professional WordPress Repair Services, Worldwide Coverage, Rapid Response](https://www.361sale.com/wp-content/themes/zibll/img/smilies/baoquan.gif)







No comments