In the WordPress development landscape, data security serves as the cornerstone for building reliable applications. Statistics reveal that over 70% of WordPress security vulnerabilities stem from insecure database operations, withSQL injectionAttacks accounted for as much as 411% of TP3T. As WordPress's core database abstraction layer, the $wpdb class provides developers with a unified interface for secure and efficient database operations. A deep understanding of the correct usage of the $wpdb class is not only a demonstration of technical proficiency but also a responsibility to safeguard user data and system security.

1. Analysis of the $wpdb Class Infrastructure and Core Methods
Global Objects and Table Prefix Mechanism
$wpdb is a globally accessible database operation object in WordPress, designed to follow the singleton pattern. An instance of this class is automatically created during WordPress initialization, encapsulating all underlying details of database interactions.
Table prefixes are a crucial component of WordPress's security architecture. By default, WordPress useswp_As a table prefix, but supports customization during installation. The $wpdb class enables$wpdb->prefixThe property provides the current table prefix via$wpdb->{table_name}Syntax for dynamic table access. For custom tables, it is recommended to use$wpdb->prefix . 'custom_table'Format the complete table name to ensure uniqueness in multi-site environments.

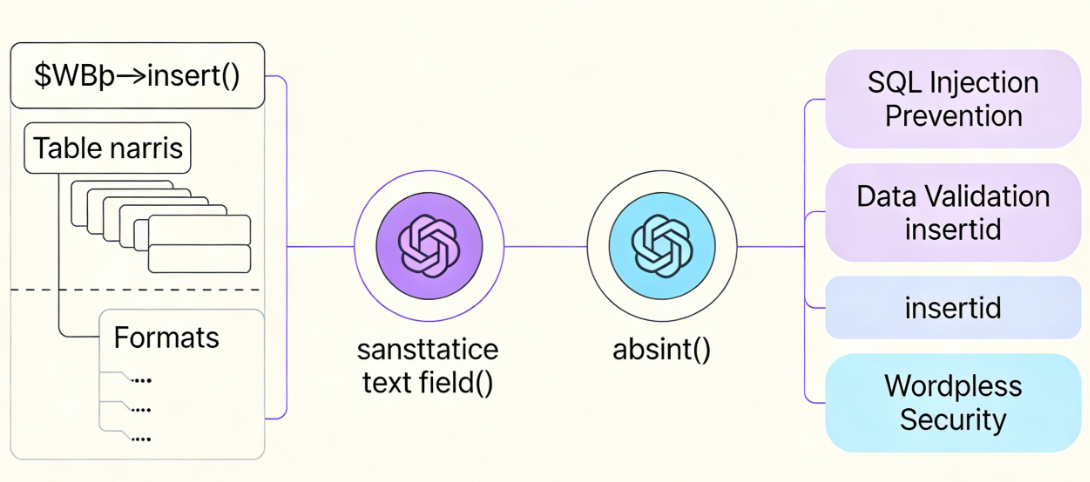
Secure Implementation Patterns for the insert Method
$wpdb->insert()The method provides a declarative approach to data insertion. It accepts three parameters: table name, data array, and format array. The format array defines the type of each data field, serving as the first line of defense against SQL injection.
Data validation should be completed before calling the insert method. WordPress provides a series of validation functions, such assanitize_text_field()Used for cleaning text input,absint()Ensure integer type security. Only validated data may enter the database operation process.
The insert method returns a Boolean value indicating whether the operation succeeded.$wpdb->insert_idThe property can retrieve the auto-increment ID of the last inserted record, a feature that proves extremely useful in scenarios requiring the identifier of a new record.
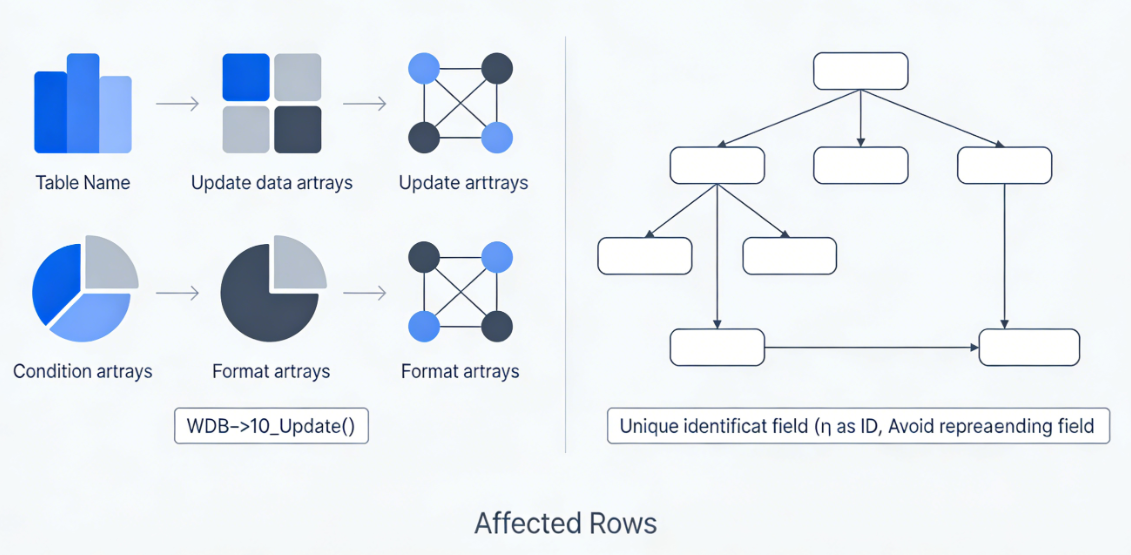
Conditional Update Strategy for the update Method
$wpdb->update()The method supports conditional update operations. It accepts four required parameters: table name, update data array, condition array, and corresponding format array. The format array must contain type definitions for both update data and condition data.
The construction of condition arrays requires careful handling. Typically, unique identifier fields such as record IDs or business-specific primary keys are used as conditions. Avoid using repeatable fields as update conditions to prevent accidental updates to multiple records.
The scope of impact of update operations can be determined by$wpdb->rows_affectedAttribute retrieval. This value reflects the actual number of records modified, which is crucial for verifying the effectiveness of the operation.
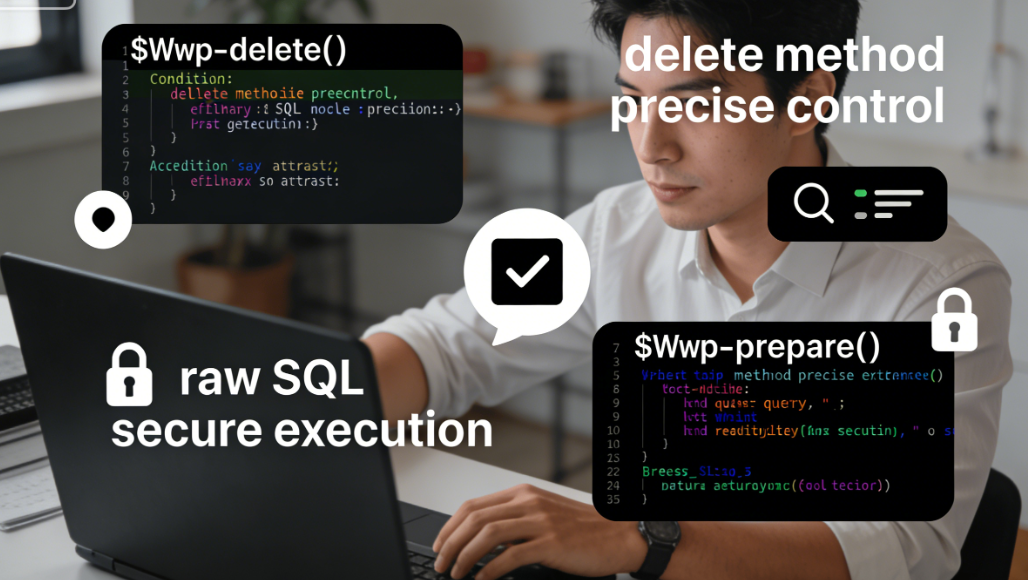
Precise deletion control of the delete method
$wpdb->delete()This method is used to remove records from a table. It accepts three parameters: the table name, a condition array, and a format array. Similar to the update method, the condition array should be sufficiently precise to ensure only the target records are deleted.
Before executing deletion operations, additional confirmation mechanisms should be implemented. Specifically, user-initiated deletion actions require confirmation dialogs or secondary verification to prevent accidental data loss. For critical data, soft deletion is recommended—marking records as deleted rather than physically removing them.
Secure execution of raw SQL in the query method
$wpdb->query()This method allows execution of raw SQL statements, which is the most flexible yet also the most dangerous approach. Use this method only when absolutely necessary, and always in conjunction with$wpdb->prepare()Perform a parameterized query.
Raw SQL statements should avoid directly concatenating user input. Any data from external sources must be treated as a potential threat and processed securely through prepared statements. This security principle should be adhered to even when data originates from "trusted" sources.
2. Multi-Layered Defense System for SQL Injection Protection
Preprocessor statementscore role
$wpdb->prepare()The method is the primary tool for defending against SQL injection. It works by separating SQL statements from parameters, ensuring parameters are properly escaped and processed through a placeholder mechanism.
Placeholder syntax supports two formats:%sFor strings,1TB 2TBFor integers,%fUsed for floating-point numbers. Correct selection of placeholder types not only ensures security but also maintains data type integrity. Database engines optimize query execution plans based on type information, enhancing query efficiency.
Prepared statements should be the standard practice for all dynamic SQL. Even seemingly simple queries can introduce security vulnerabilities due to special characters or encoding issues. Consistently using prepared statements eliminates this type of risk.

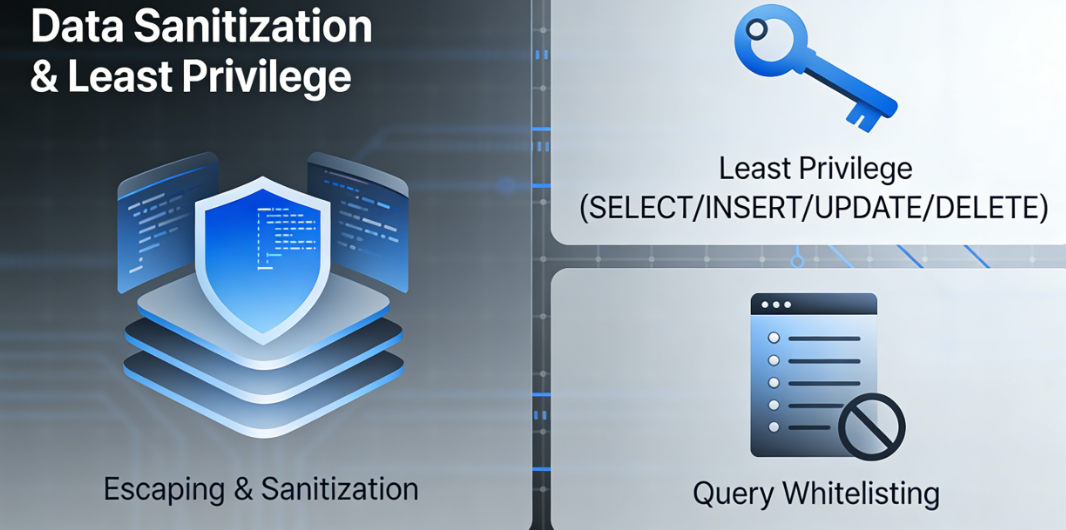
Data EscapingBest Practices for Cleaning
Beyond preprocessing statements, WordPress also provides a multi-level data cleansing mechanism.esc_sql()The function provides additional escape protection for specific scenarios, particularly when constructing complex query conditions.
Input validation should occur early in the data processing stage.filter_input()respond in singingfilter_var()The function provides a standardized input filtering mechanism that can validate common data types such as email addresses, URLs, and integer ranges.
Output escaping serves as another crucial line of defense. Select the appropriate escaping function based on the output context:esc_html()For HTML content,esc_url()For URLs,esc_attr()For HTML attributes. These functions prevent cross-site scripting attacks and protect end-user security.
Implementation of the Principle of Least Privilege
Database user permissions should adhere to the principle of least privilege. WordPress application database users typically only require SELECT, INSERT, UPDATE, and DELETE permissions, and do not need administrative privileges such as DROP or ALTER.
In plugins or themes, avoid using database connections with elevated privileges. If you must perform operations that alter table structures, use a separate, strictly restricted database connection and close it immediately after the operation is complete.
The whitelist mechanism can further restrict the scope of database operations. For user-provided query parameters, verify whether they fall within the permitted value range and reject inputs that do not meet expectations.
3. Transaction Processing and Data Consistency Assurance
Fundamental Concepts and Application Scenarios of Transactions
A database transaction is an indivisible sequence of database operations. The ACID properties of transactions—atomicity, consistency, isolation, and durability—ensure data integrity and reliability.
In WordPress development, transactions are particularly suitable for scenarios requiring data consistency maintenance. User registration processes may involve insert operations across multiple tables, financial transactions demand precise balance updates, and content publishing may involve multiple metadata records. These scenarios should all utilize transactions to ensure the integrity of operations.
Transaction Implementation Patterns in WordPress
even though$wpdb ClassNo dedicated transaction methods are provided, but transaction control can be achieved by executing SQL statements directly.START TRANSACTION,COMMITrespond in singingROLLBACKThe statement provides full transaction management capabilities.
Transaction implementation should incorporate an exception handling mechanism. Enclose transaction code within try-catch blocks to execute rollback operations upon error occurrence, ensuring database consistency. Transaction logs must meticulously document operational details to facilitate troubleshooting and audit trail tracking.
Nested transactions require special handling. MySQL does not support true nested transactions, but similar behavior can be simulated through the savepoint mechanism. Complex transaction logic should be carefully designed to avoid deadlocks and prolonged table locks.
Transaction Performance Optimization Strategies
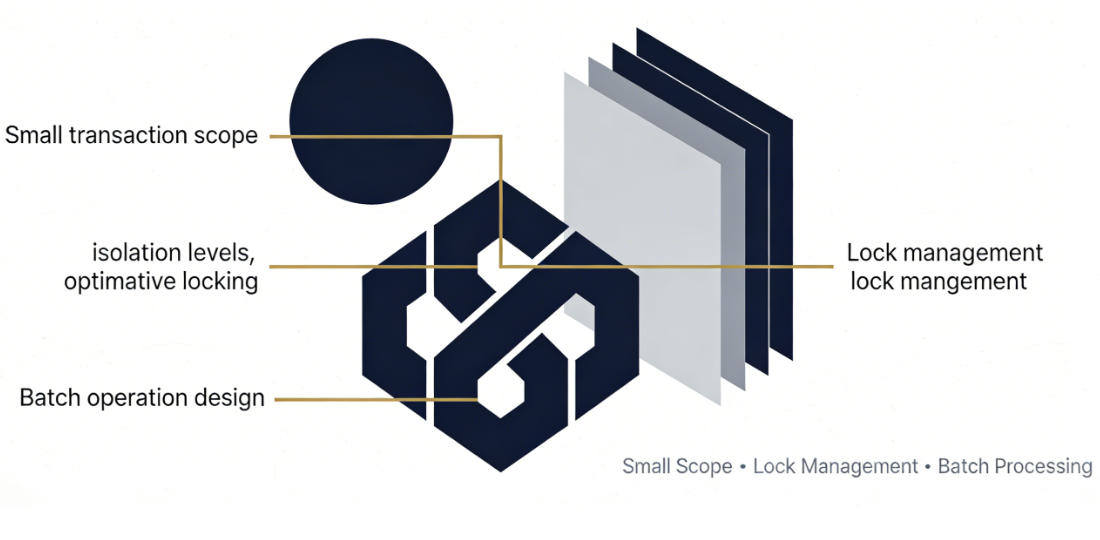
Transaction scope should be kept as small as possible. Long-running transactions consume database resources and impact system concurrency performance. Only include necessary operations within transactions, completing and committing them quickly.
Lock management is a critical factor in transaction performance. Select an appropriate isolation level based on business requirements to balance data consistency and system performance. In scenarios with frequent reads and infrequent writes, consider using optimistic locking to reduce lock contention.
Batch transaction processing requires special design. Insertion or update operations involving large volumes of data should be performed in batches, with each batch using an independent transaction to avoid performance issues caused by overly large individual transactions.
4. Implementation Strategies for Cross-Database Compatibility
Abstract Handling of Database Differences
Different database systems exhibit variations in SQL syntax, functions, and data types. The $wpdb class masks these differences through an abstraction layer, but developers should remain mindful of common incompatibility issues.
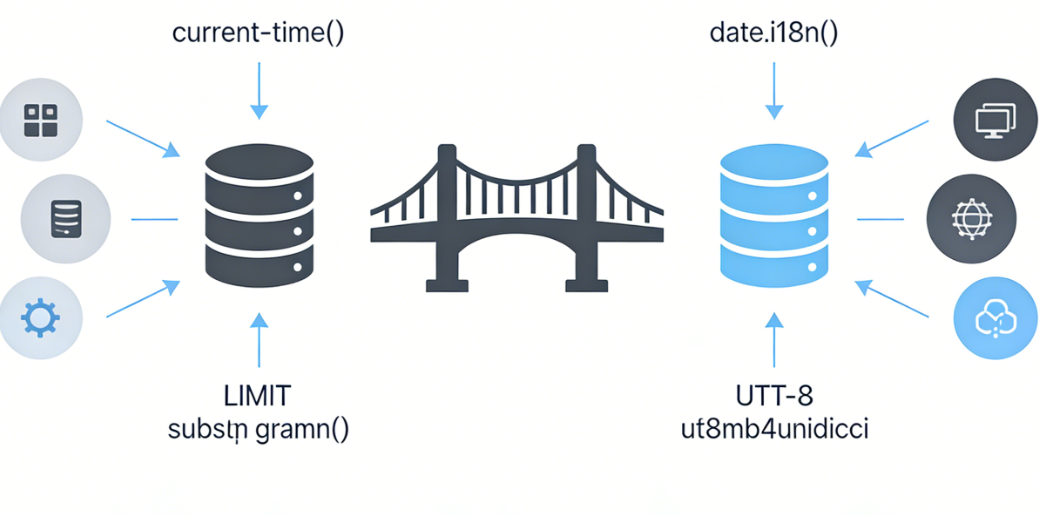
Date and time handling presents common compatibility challenges. MySQL's date functions may differ from other database systems; you should use the date functions provided by WordPress, such ascurrent_time()respond in singingdate_i18n()Ensure cross-platform consistency.
Special attention must be paid to the syntax differences in the LIMIT clause. MySQL usesLIMIT offset, countSyntax, while other databases may use different formats. The $wpdb class has already addressed this difference, but compatibility must be considered when writing SQL directly.
Consistency of Character Set and Collation Rules
Character set settings affect data storage and comparison. WordPress defaults to the UTF-8 character set, which is the most universal choice. Ensure all custom tables use the same character set configuration to avoid garbled text and sorting issues.
Sorting rules determine how strings are compared and sorted.utf8mb4_unicode_ciThis is the recommended sorting rule, supporting the full Unicode character set and providing predictable sorting behavior. Multilingual websites should pay particular attention to selecting the appropriate sorting rule.
Query PerformanceCross-platform optimization
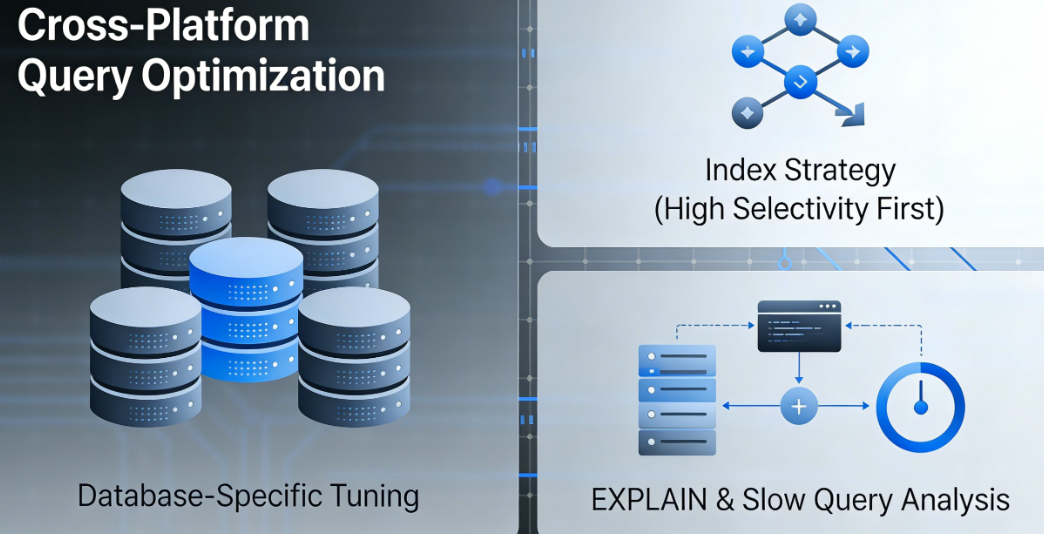
Query optimizers in different database systems operate in distinct ways. Writing efficient SQL requires consideration of the target database's characteristics.
Indexing strategies should be designed based on query patterns. Analyze common query conditions and create indexes for frequently used fields. For composite indexes, consider the field order and place fields with high selectivity at the beginning.
Query execution plan analysis is a crucial means of optimization. UseEXPLAINMonitor the execution process of statement comprehension queries to identify performance bottlenecks. Regularly review and optimize slow queries to maintain system performance levels.
5. Professional Methods for Debugging and Error Handling
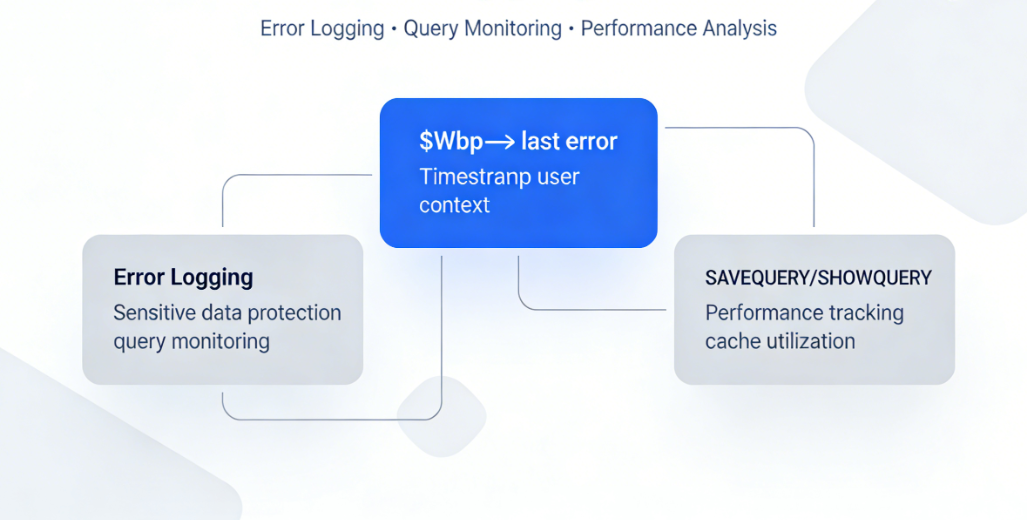
Proper Documentation of Error Messages
$wpdb->last_errorThe property provides the last SQL error message. In development environments, displaying this information can aid debugging, but in production environments, errors should be logged to a file rather than displayed directly to users.
Error logs should contain sufficient contextual information: timestamps, user IDs, executed operations, relevant parameters, etc. This information is critical for troubleshooting and security audits. Avoid logging sensitive information such as passwords or personally identifiable information.
Query Monitoring and Performance Analysis
SAVEQUERYrespond in singingSHOWQUERYTracking and displaying constant-controlled queries. When debugging complex data operations, enabling query logging can help understand the database interaction patterns of your code.
Performance monitoring should focus on query execution time and resource consumption. Pay particular attention to slow-executing queries and frequently executed queries, as these are key targets for performance optimization. WordPress's caching mechanisms can significantly reduce database load; leveraging object caching and page caching appropriately enhances system performance.
Recovery Strategy for Abnormal Conditions
Database connection failures should be handled with appropriate recovery mechanisms. Temporary network issues can be resolved through retry mechanisms, while persistent failures require switching to a backup system or providing degraded services.
Detecting and repairing data corruption is a critical aspect of system robustness. Regular data consistency checks can identify potential issues, while automated repair scripts can resolve common data problems without disrupting service.
Backup and recovery strategies serve as the ultimate safeguard for data security. An automated backup system should encompass data from custom tables, and the recovery process must undergo thorough testing to ensure reliable execution during emergencies.
6. Security Audits and Continuous Improvement
Security Focus Areas in Code Review
During code reviews, database operations should be a key focus. Reviewers must verify that all dynamic SQL uses prepared statements and that input data undergoes proper validation and escaping.
The establishment and enforcement of secure coding standards help unify security practices across teams. These standards should explicitly prohibit insecure patterns such as direct concatenation of SQL statements and the use of deprecated functions.
Security Updates for Dependent Components
The $wpdb class, as a core WordPress component, will be improved with WordPress updates. Keeping your WordPress system updated ensures you receive the latest security fixes and performance enhancements.
Third-party libraries and frameworks may introduce database operation components. The security and compatibility of these components must be evaluated to ensure they meet the project's security standards.
Automated Implementation of Security Testing
Automated security testing should be implemented early in the development process. Static code analysis tools can detect common security vulnerability patterns, while dynamic security scans simulate attack behavior to validate system defenses.
Penetration testing is regularly conducted by professional security teams to uncover complex vulnerabilities that automated tools may overlook. Test results should be documented in detail, with progress tracked for the remediation of each identified issue.
The continuous cultivation of security awareness is the fundamental guarantee for long-term security. Regular security training, technical sharing, and case studies help team members maintain vigilance against security threats and master the latest protective technologies.
By implementing secure operations for the $wpdb class through a systematic approach, developers can build robust and secure WordPress applications. Security is not a one-time task but an ongoing process requiring continuous attention and improvement. In today's world where data value grows increasingly critical, the level of emphasis placed on database operation security directly determines an application's reliability and user trust.
Link to this article:https://www.361sale.com/en/82438The article is copyrighted and must be reproduced with attribution.

















![Emoji[wozuimei]-Photonflux.com | Professional WordPress repair service, worldwide, rapid response](https://www.361sale.com/wp-content/themes/zibll/img/smilies/wozuimei.gif)
![Emoticon[baoquan] - Photon Wave Network | Professional WordPress Repair Services, Worldwide Coverage, Rapid Response](https://www.361sale.com/wp-content/themes/zibll/img/smilies/baoquan.gif)







No comments